Vulnerabilities In Software Defined Networks Research.
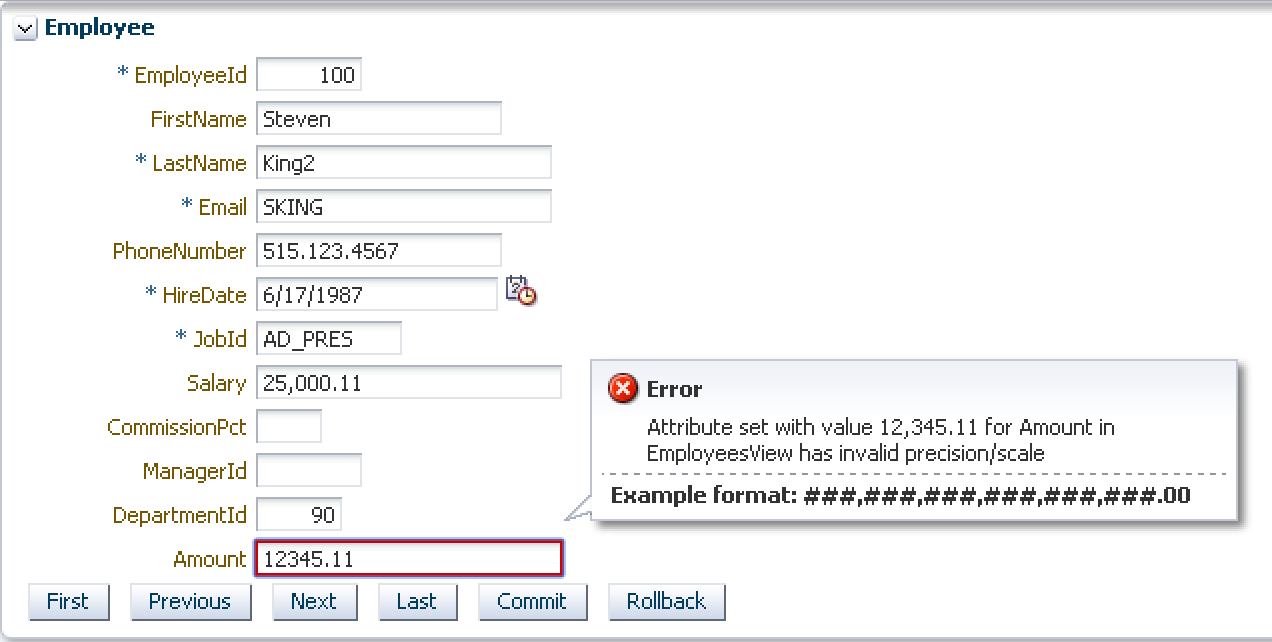
Vulnerabilities are considered to be weaknesses in hardware that allow an attacker to compromise the availability, integrity, or confidentiality of that software or the data it handles. Some of the vilest vulnerabilities permit attackers to abuse a compromised computer, producing it to run random code without the user's information.
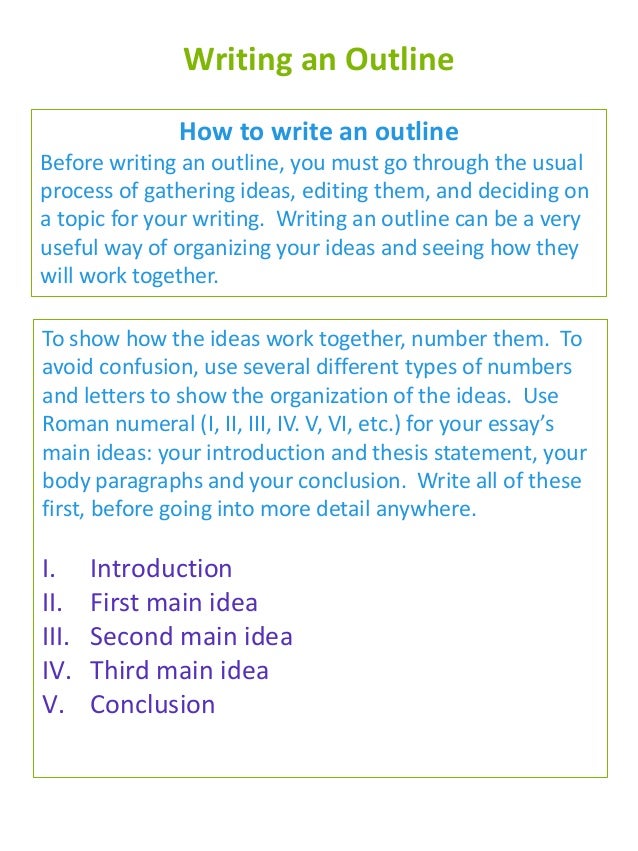
Here is a list of best free research paper writing software for Windows. These are basically the word processor software which are used to create various academic documents which include research papers too. You can also create thesis, reports, journal articles, dissertations, and more such documents using these free software.
This paper discusses 21 issues related to security with respectiveto requirement that can eliminate vulnerabilities at the early development of life cycle. By keeping these issues at back of mind, working people in the area of software security can able to build more secure software and also the goals of security can easily be identified.
Other posts on the site.
Abstract: we propose an effective approach to obtain software security vulnerabilities in web with vertical search technique in this paper. We use a keyword-trainer to get domain keywords in software security domain. Then the web page filter is designed after analyzing the obtained domain keywords and the structure of the URL topology.
It is when most, if not all, attacks will occur on a network. When attackers find vulnerabilities they can break through the security relatively quickly, and if they are not stopped they can damage a network extremely. Disclosure time is the vulnerability is disclosed when the discoverer reveals details of the problem to a wider audience.
In computer security, a vulnerability is a weakness which can be exploited by a threat actor, such as an attacker, to perform unauthorized actions within a computer system. To exploit a vulnerability, an attacker must have at least one applicable tool or technique that can connect to a system weakness.
Zero-Day Vulnerabilities, Exploits and Attacks: A Complete Glossary. All software contains bugs. Vulnerabilities are special type of bugs that enable attackers to leverage software for malicious purposes, such as gaining remote control of a machine, escalating privileges, carrying out lateral movement, and more.